
Managed NDR
Network Detection & Response
Managed NDR
Network Detection & Response
Detect and combat cyber attacks by analyzing network traffic
For a long time, IT protection was synonymous with preventive measures such as securing access. Today, this alone is no longer sufficient – once the protective wall has been breached, the attacker can move around the network unhindered. That's why modern, comprehensive network monitoring solutions are needed.
Analyzing network traffic and making it visible
In today's threat environment, the question is not whether a company will be breached by a cyberattack, but when the attack will occur. By analyzing network traffic (NTA) and monitoring all activity, attacks are visible early, security issues are identified, anomalies are detected, the attack surface is minimized, and security is thus enhanced.
Monitor all operations and devices with NDR
An NDR solution provides a complete view of the entire network infrastructure in real time, including all hosts and accounts, laptops, servers, routers, switches and firewalls, IoT devices, virtual assets and cloud identities. It analyzes and correlates the myriad of operations (events) and security information. Artificial intelligence and sophisticated machine learning algorithms help to focus on relevant events and immediately follow up on behavior-based anomalies (use cases), even if a breach has already occurred.
Identifying hazards requires the right sources – and adequate means to identify «high-risk events» from the mass of data, filter out false positives, and respond quickly. «Detection and Response» must always be considered together:
- Detect the relevant events
- Contain, isolate and prevent further propagation
- Prompt, complete elimination
- Recovery: get back to normal, incorporate improvements
SOC Jump Start: Your easy start with NDR
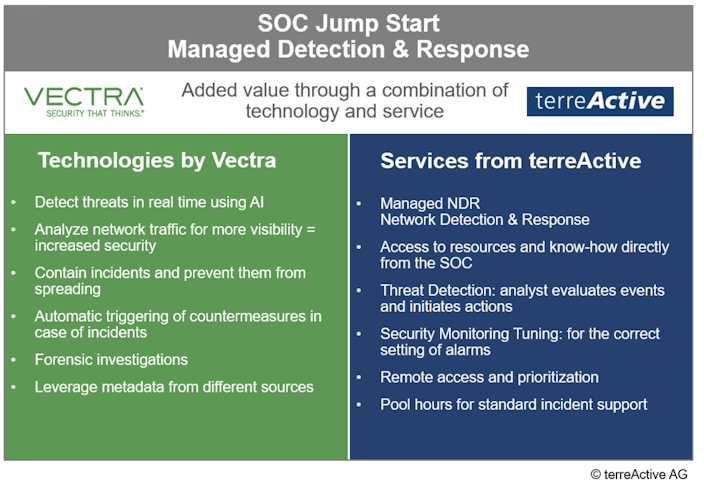
Innovative technology and customized services
The package includes the technology of the Vectra Cognito platform and SOC services from terreActive, and in this combination helps to quickly detect and combat threats. This allows you to continuously optimize your cyber security posture.
The Managed Network Detection & Response Package:
Engineering & SOC Support
- SOC portal access, hotline, remote access, resource planning of the analysts and definition of their priorities.
Threat Detection
- Sighting and assessment by an analyst, initiation of countermeasures or forwarding of the incident to a Tier 2 analyst for further clarification.
Security Monitoring Tuning
- Setting and tuning of all alarms for proper detection and avoidance of false alarms.
Pool hours for incidents
- Pool system to cover variable efforts for analysis, changes and general support as well as for uncomplicated billing.
Knowledge and experience of competent specialists
When a company lacks the resources and the necessary know-how, it pays to call in the specialists of a Security Operations Center (SOC).terreActive has been designing, integrating and operating cyber security solutions for 25 years and protects the critical IT security infrastructures and corporate data of well-known Swiss customerswith its ISO-certified SOC services.terreActive is a long-standing partner of Vectra.
Vectra Cognito: NDR solution for network threat detection
The Vectra Cognito platform automatically monitors and analyzes all traffic to immediately detect and adequately respond to suspicious activity on the internal network as well as traffic from the data center to the Internet. The platform uses advanced analytics, rule-based detection, and AI-based machine learning to detect specific patterns of the attackers behavior.
Vectra Cognito is used by companies and organizations of different sizes – financial institutions, insurance companies, universities, energy suppliers, technology companies, as well as government and healthcare organizations. By anyone who wants to detect threats and stop them before damage is done.
Real-time identification and countermeasures
Vectra Cognito monitors the behavior of all physical and virtual hosts and all accounts (cloud identities):
- Analysis of the interactions of security data and enriched metadata from various sources
- Automatic real-time detection of covert attacks by combining machine learning, data science and behavioral analysis
- Definition of rules for responding to dynamic incidents and automatic triggering of countermeasures (response)
- Key threat hunting and forensic investigation of incidents
Vectra as visionary and market leader
The market research institute Gartner maintains a «Magic Quadrant» for intrusion detection and prevention systems and positions Vectra as a «visionary» in one of their reports. The latest Gartner Market Guide for Network Detection and Response (NDR)ranks Vectra as a market leader.
If you have questions about your network security or would like to learn more about terreActive's services, contact us without obligation.
Would you like a live demonstration of the Vectra Cognito platform? We make it possible.
