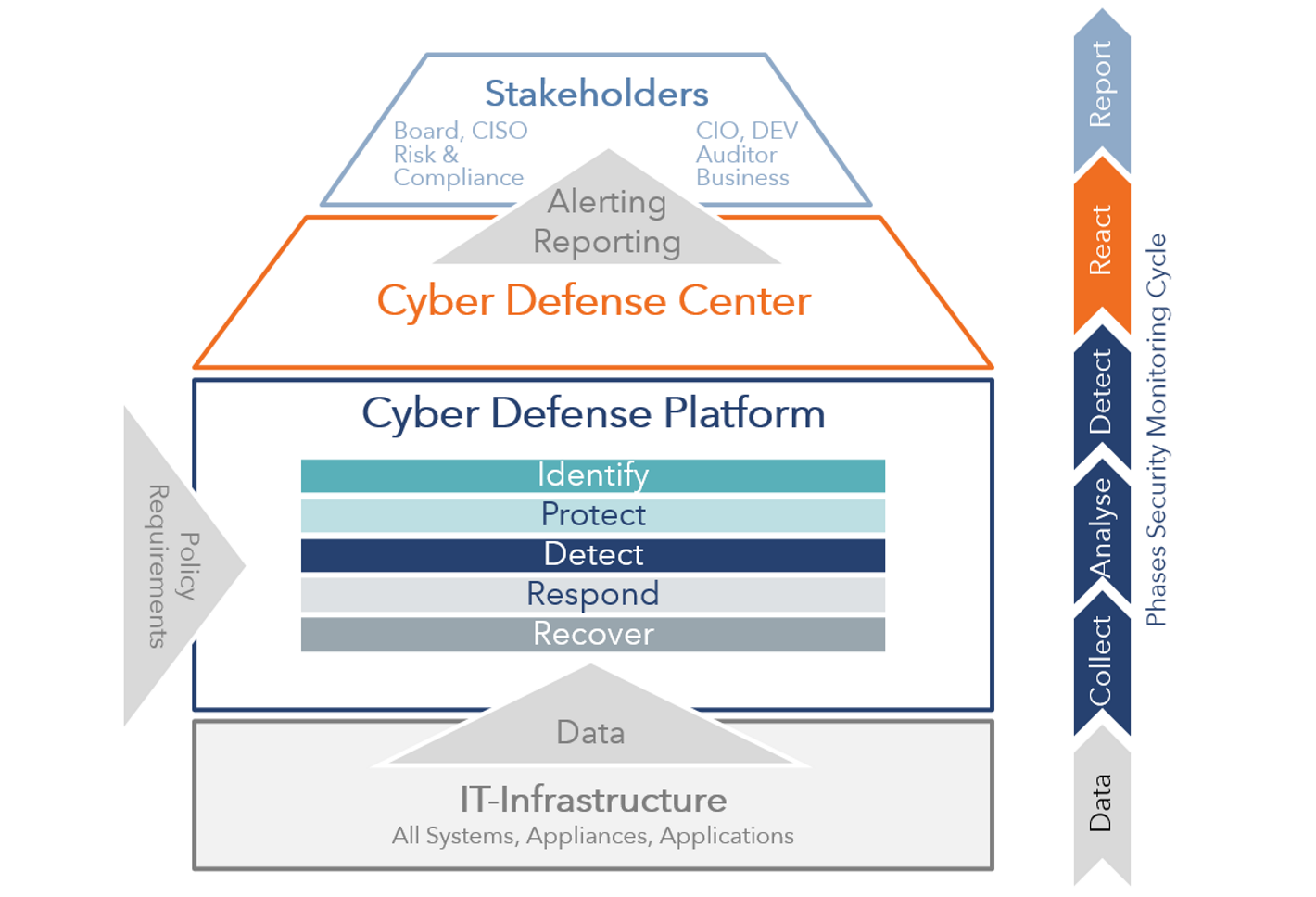
The Cyber Defense Solution
The Cyber Defense Solution consists of various technical components and organizational units with different functions and tasks. Only the optimal coordination results in an overall structure that offers you real protection against cyber attacks.
The target for effective defence
What should your solution look like?
terreActive recommends this tried-and-tested solution structure.
The IT infrastructure
The IT infrastructure to be monitored forms the basic platform of the solution. This refers to all systems, appliances and applications that are available for the provision of business-critical applications and for the protection of the infrastructure. They provide valuable information in the form of machine data (e.g. log data) to the central Security Monitoring Framework.
SIEM: The Security Monitoring Framework
The core of the security monitoring solution is the framework, where all data is collected and stored. During baselining, the normal state is defined so that deviations can be determined later. In the framework, the data is also correlated and forwarded for analysis as predefined events, so-called customer-specific use cases.
The Security Operations Center
Security incidents detected by monitoring are processed in SOC by a CERT (Computer Emergency Response Team). The experts take care of verification and follow-up, which varies according to the event and is defined in processes. In larger organizations, this function is performed by a separate team within the security department. This separation of powers means an additional safety benefit and relieves the company organization.
Good visualization helps for fast detection - and speed can be crucial in the event of a cyber attack. A good security monitoring solution supports the SOC by concentrating the most important data in graphically prepared dashboards. At the same time, the data can be used to generate reports or for analysis and causal research.
The Stakeholders
Through the centralized security monitoring approach, the data, or the reports from it, can be made available to a large number of interest groups in an appropriate form. Every stakeholder - whether technically adept, compliance-oriented or a member of the Executive Board - receives his report in a form that he can understand. The range of people interested in the reports can go far beyond IT security and includes, among others, application managers, development and business owners.